South Africa Cybersecurity Market Analysis by ���ϲ�����
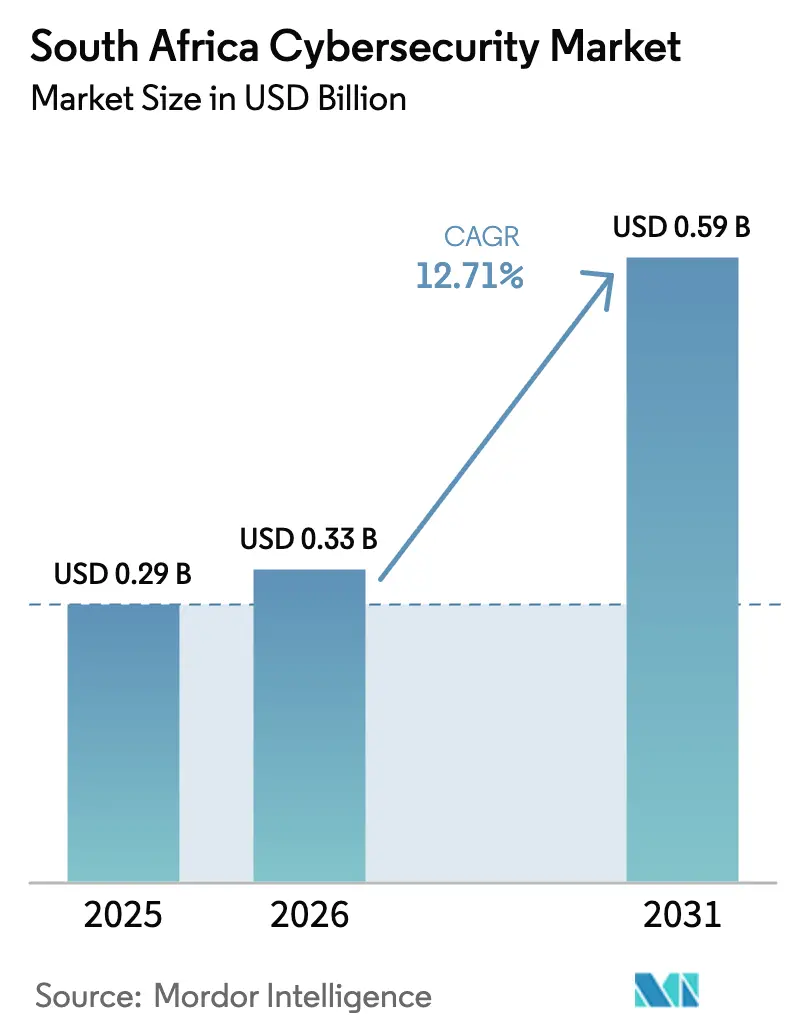
The South Africa cybersecurity market size is expected to grow from USD 0.29 billion in 2025 to USD 0.33 billion in 2026 and is forecast to reach USD 0.59 billion by 2031 at 12.71% CAGR over 2026-2031. Spending momentum is accelerating as regulators tighten breach-reporting rules, enterprises modernize legacy networks, and adversaries weaponize automation to bypass perimeter defenses. Large financial institutions now earmark double-digit portions of IT budgets for layered security, while hyperscale data-center builds in Johannesburg and Cape Town are steering cloud-security purchasing toward zero-trust frameworks. Skills shortages persist, so managed detection and response contracts are rising quickly, especially among small and medium enterprises looking for 24/7 coverage. Finally, data-localization clauses in the National Data and Cloud Policy are shaping hybrid architectures that blend on-premise controls with cloud-native analytics, adding complexity but also lifting long-term vendor revenues.
Key Report Takeaways
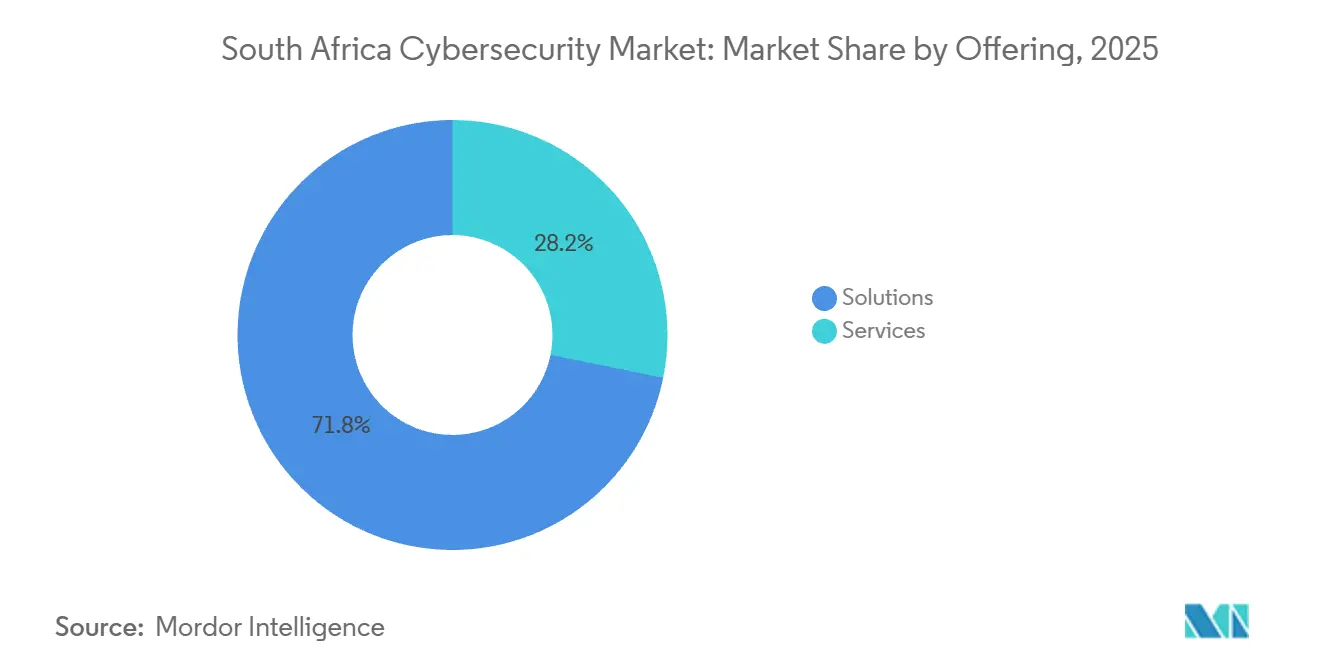
- By offering, solutions captured 71.81% market share in 2025, while services are projected to grow at a 13.43% CAGR through 2031.
- By deployment mode, on-premise held 57.28% of the South Africa cybersecurity market share in 2025, whereas cloud-based security is set to advance at a 13.64% CAGR over 2026-2031.
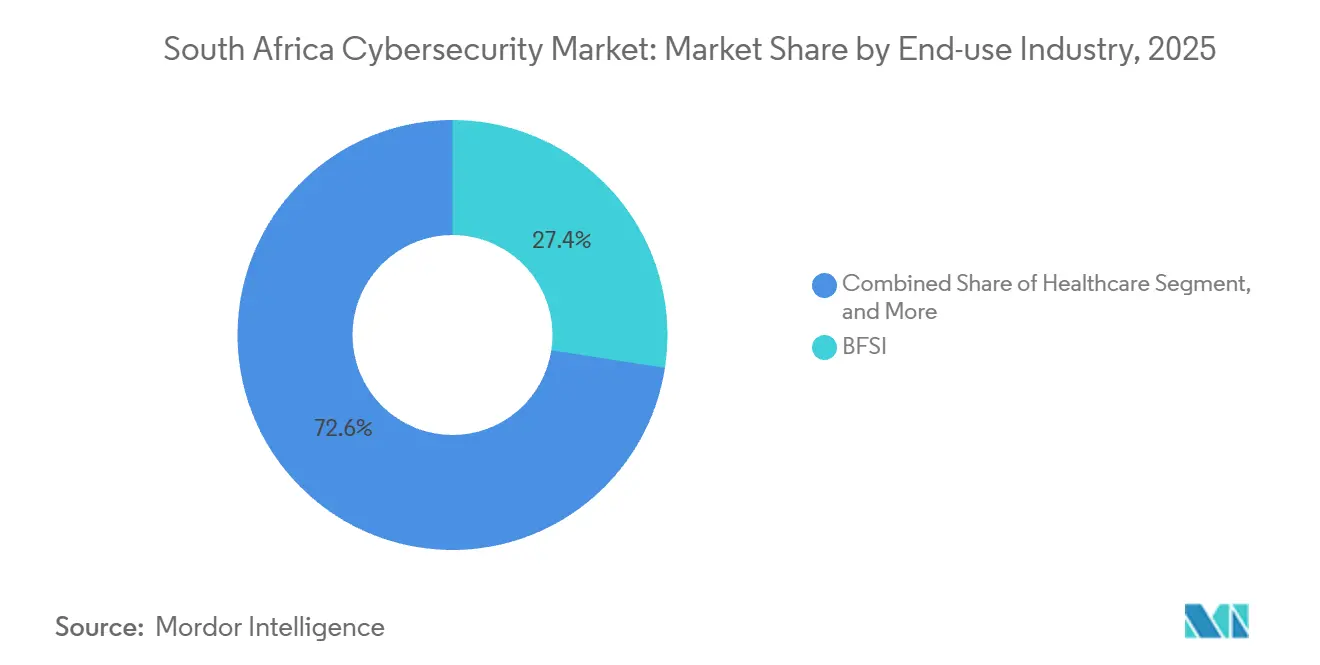
- By end-use industry, banking, financial services, and insurance led spending with 27.44% share in 2025, but healthcare is forecast to expand at a 14.11% CAGR to 2031.
- By enterprise size, large enterprises generated 63.87% of the share in 2025, although SMEs are anticipated to register a 13.75% CAGR due to the growing demand for security-as-a-service.
Note: Market size and forecast figures in this report are generated using ���ϲ�����’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
South Africa Cybersecurity Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Escalating Cyber Threat Landscape Targeting SA Financial Institutions and SOEs | +3.2% | National, concentrated in Gauteng and Western Cape financial hubs | Short term (≤ 2 years) |
| Enforcement of Cybercrimes Act 2021 Driving Compliance Investment | +2.8% | National, heightened focus in BFSI and public sector | Medium term (2-4 years) |
| Hybrid Work and Cloud Migration Accelerating Zero-Trust Adoption | +2.4% | National, early uptake in Johannesburg, Cape Town, Durban metro areas | Medium term (2-4 years) |
| Expansion of Hyperscale Data Centers in Johannesburg and Cape Town | +1.9% | Gauteng and Western Cape, spillover to regional connectivity hubs | Long term (≥ 4 years) |
| Rapid Growth of Mobile Money and Township E-commerce Boosting Demand for Security | +1.5% | National, township economies in Gauteng, KwaZulu-Natal, Eastern Cape | Medium term (2-4 years) |
| Cyber-Insurance Premiums Linked to Maturity of Controls | +0.9% | National, large enterprises and financial institutions | Long term (≥ 4 years) |
| Source: ���ϲ����� | |||
Escalating Cyber Threat Landscape Targeting SA Financial Institutions and SOEs
South African banks and state-owned enterprises endured a marked rise in ransomware and business-email-compromise attempts during 2024-2025, with SABRIC logging a 34% year-on-year increase in attacks on payment gateways and customer databases.[1]South African Banking Risk Information Centre, “Annual Crime Statistics Report 2024,” sabric.co.za Organized crime groups leveraged infrastructure in neighboring countries, prompting banks to deploy advanced endpoint detection, network segmentation, and 24/7 security-operations centers. Transnet’s 72-hour outage at Durban harbor in July 2024 highlighted operational risks to critical logistics, spurring mandated audits across all SOEs. Directive 8/2024 now obliges financial institutions to report breaches inside 24 hours, cementing cybersecurity as a non-negotiable budget line. Insurers responded by withholding ransomware cover unless clients prove multi-factor authentication and offline backups, further reinforcing spending discipline.
Enforcement of Cybercrimes Act 2021 Driving Compliance Investment
The Cybercrimes Act criminalizes negligent security, and prosecutions initiated in 2024 signaled a new era of accountability.[2]Department of Justice and Constitutional Development, “Cybercrimes Act 19 of 2020: Enforcement Guidelines,” justice.gov.za POPIA also requires breach notification within 72 hours, and the Information Regulator issued 18 enforcement notices with fines totaling ZAR 12 million in 2025.[3]Information Regulator South Africa, “Enforcement Notices and Penalties 2025,” justice.gov.za/inforeg Enterprises, therefore, audit vendor postures, embed indemnity clauses, and invest in data-loss-prevention, encryption, and GRC platforms. Retailers and healthcare operators have felt the sting first, motivating board-level oversight of security budgets. Legal-tech providers are surfacing to translate overlapping mandates into actionable controls for resource-constrained SMEs.
Hybrid Work and Cloud Migration Accelerating Zero-Trust Adoption
A 2025 PwC study found that 61% of local companies intend to be “mostly cloud” within 2 years, yet only 38% have rolled out identity-based access controls. This misalignment spurs interest in zero-trust network access frameworks that authenticate every user and device before granting application access. The Reserve Bank’s March 2025 consultation paper on cloud computing for financial institutions references Singaporean outsourcing standards, effectively codifying the principles of least privilege and continuous authentication. Vendors now embed zero-trust features inside secure-access-service-edge bundles, positioning them as compliance enablers. Data-localization rules are meanwhile creating hybrid estates where on-premises identity providers synchronize with cloud-based analytics, elevating orchestration complexity but also creating vendor opportunities.
Expansion of Hyperscale Data Centers in Johannesburg and Cape Town
Teraco’s 40-megawatt JB7 facility, commissioned in 2024 for ZAR 8 billion (USD 440 million), sets new benchmarks for biometric access and SOC 2 compliance. Microsoft committed another ZAR 5.4 billion (USD 297 million) in 2025 to deepen Azure capacity, while Google Cloud’s Johannesburg region went live in January 2024. Workloads are consolidating into a handful of fortified sites, driving adoption of cloud-native firewalls, container security, and serverless protection. Concentration also elevates the threat profile, so regulators are considering geographic redundancy mandates that would further stimulate spend on cross-provider fail-over tooling.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Shortage of Advanced Cybersecurity Skills in South Africa | -2.1% | National, acute in Gauteng, Western Cape, and KwaZulu-Natal | Long term (≥ 4 years) |
| Budget Constraints Amid Weak Macroeconomy | -1.6% | National, heavier on public sector and SMEs | Medium term (2-4 years) |
| Load-Shedding Impact on On-Premise Security Appliance Uptime | -0.8% | National, especially areas with aging grid infrastructure | Short term (≤ 2 years) |
| Fragmented Regulatory Guidance Across POPIA, Cybercrimes Act And International Standards | -0.6% | National, burdensome for SMEs and cross-border operators | Medium term (2-4 years) |
| Source: ���ϲ����� | |||
Shortage of Advanced Cybersecurity Skills in South Africa
Industry bodies estimate more than 30,000 unfilled cyber roles across the continent, with South Africa absorbing a large share. Wage inflation tops 15% annually for Certified Information Systems Security Professionals, pushing enterprises toward managed services. Brain drain remains pronounced as newly certified talent migrates to Europe and the Middle East within two years. Outsourcing eases the gap but raises vendor-lock-in risk and erodes internal know-how. Government training programs are helpful yet underfunded compared with demand, so the talent deficit will persist beyond 2031.
Budget Constraints Amid Weak Macroeconomy
GDP growth averaged below 1.5% in 2024-2025, squeezing capital expenditure for both public agencies and SMEs. Many municipalities postponed firewall and SIEM upgrades, while small firms rely on consumer-grade tools that falter against targeted attacks. Credit conditions remain tight, making hardware leases difficult, and cyber-insurance premiums rose 22% in 2025, adding another hurdle. This divergence widens the security gap between well-funded banks and under-protected suppliers, creating systemic exposure along supply chains.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Segment Analysis
By Offering: Outsourcing Propels Services Growth
Solutions dominate the market with a 71.81% share in 2025 as enterprises purchased endpoint, application, and network protection to defend hybrid estates. Services, though smaller, are the fastest-growing segment at a 13.43% CAGR because the South African cybersecurity market depends on external expertise to bridge its talent gap. Financial institutions use professional services for penetration tests that comply with Directive 8/2024, while managed detection and response subscriptions provide round-the-clock monitoring without staffing a security operations center. Identity and access management, along with cloud workload protection, outpace legacy perimeter firewalls as zero-trust strategies mature. Integrated risk-management dashboards that condense alerts into business context are gaining board-room visibility, especially when insurers demand proof of control maturity before underwriting.
The South African cybersecurity market for services will continue to expand as compliance audits, digital forensics investigations, and incident response retainers become embedded in operational budgets. Application-security spending spreads as DevSecOps pipelines embed static and dynamic code checks earlier in release cycles. Encryption and data-loss prevention tools see uptake in healthcare and retail to protect sensitive personal data under POPIA. Meanwhile, infrastructure protection revenue grows more slowly because virtual appliances replace hardware, cutting refresh cycles. Vendors able to deliver turnkey consulting, deployment, and 24/7 managed operations under one contract are best placed to capture wallet share.
By Deployment Mode: Hybrid Strategies Tilt Toward Cloud
On-premise controls retained 57.28% of share in 2025 because government data-localization mandates restrict sensitive workloads. Yet cloud-delivered security is expected to post a 13.64% CAGR as the Reserve Bank clarifies that public cloud is permissible if residency and audit rights are contractually enforced. The South Africa cybersecurity market size linked to cloud services will therefore expand faster than traditional appliance refreshes. Large banks now route non-core workloads such as email hygiene through secure-access-service-edge platforms hosted in Johannesburg zones. SMEs favor subscription models that avoid capital outlay, driving adoption of managed detection and response delivered from hyperscale facilities.
Hybrid architectures dominate among top-tier enterprises that maintain on-premise identity stores but pipe logs into cloud-native analytics platforms. The South Africa cybersecurity market share for hybrid deployments is poised to rise as sovereign cloud offerings let public agencies meet localization rules without building data centers. Resiliency planning gains urgency because load-shedding continues to threaten on-premise uptime, prompting more firms to tap cloud-based failover. Vendors packaging compliance templates, evidence collection, and automated audit reports into their cloud portfolios gain an edge with regulated buyers.
By End-Use Industry: Digital Health Spurs Fastest Uptick
BFSI remained the largest segment with 27.44% share in 2025, rooted in strict oversight and lucrative attack surfaces. Healthcare is the fastest-growing sector, with a 14.11% CAGR, as electronic health record rollouts and telemedicine proliferate. High-profile ransomware events that froze hospital operations pushed provincial departments to earmark emergency funds for endpoint isolation and immutable backups. Retailers are modernizing payment-card defenses as township e-commerce flourishes, while industrial firms reinforce operational-technology networks against sabotage. Telecom operators upgrade cloud firewalls and API security to protect 5G and fiber investments, though their growth tracks just under the market average.
Across verticals, the South Africa cybersecurity market size grows whenever sector regulators issue new minimum-control checklists, as seen in finance and healthcare. Conversely, fragmented guidance between POPIA, the Cybercrimes Act, and ISO frameworks complicates strategy for mid-market players, spurring uptake of turnkey compliance platforms. Sector-specific playbooks such as HITRUST-mapped templates for hospitals are emerging differentiators for service providers.

By Enterprise Size: SMEs Accelerate Security-As-A-Service Uptake
Large organizations captured 63.87% of share in 2025 because they run complex multi-cloud estates and face intense regulatory scrutiny. However, SMEs will record the highest growth, advancing at 13.75% as insurers discount premiums when minimum controls are proven. The South African cybersecurity market share tied to SMEs is small today but is growing rapidly due to affordable, cloud-hosted bundles that combine endpoint, email, and web defense in a single subscription. SABRIC awareness campaigns helped smaller firms adopt multi-factor authentication, and vendor channel programs now target resellers serving secondary cities.
Large enterprises still invest heavily in security orchestration, automation, and response platforms to tame alert volumes. Their geographic clustering in Gauteng and the Western Cape creates demand hubs for consultants and managed service providers. Yet complexity is their Achilles heel, as sprawling supply chains introduce third-party risk. Vendors offering consolidated platforms that cover identity, endpoint, network, and cloud controls in a single console are gaining traction among resource-stretched security teams.
Geography Analysis
Gauteng and the Western Cape accounted for the largest market share in 2025 because financial headquarters, asset managers, and hyperscale data centers are concentrated in Johannesburg and Cape Town. Gauteng alone accounts for the largest slice of the South African cybersecurity market, with banks funding security operations centers, threat intelligence feeds, and zero-trust pilots to protect payment systems. Western Cape trails closely; its fast-growing tech start-up scene and insurance cluster drive cloud-security adoption above the national average, as firms leverage Azure and Google Cloud zones nearby. Hyperscale expansion is driving demand for container security, key management services, and API shielding tools.
KwaZulu-Natal is emerging as a secondary growth pole thanks to the Port of Durban’s digitization and a thriving business-process outsourcing sector that requires compliance with European data laws. Local talent scarcity means many firms procure managed detection from Gauteng providers, but new university programs in Durban are beginning to feed a regional pipeline. The remaining provinces Eastern Cape, Free State, Limpopo, Mpumalanga, Northern Cape, and North West collectively represent a modest share of the South Africa cybersecurity market. Spending here centers on municipalities, hospitals, and universities that often rely on baseline antivirus and perimeter firewalls. Data-localization mandates are, however, prompting regional colocation providers to pitch sovereign-cloud services that comply with POPIA yet avoid heavy capital expenditure for public bodies.
Cross-border links into Botswana, Namibia, and Mozambique elevate the need for secure SD-WAN and VPN encryption as firms transmit sensitive data across borders lacking POPIA-grade privacy statutes. The Southern African Development Community’s draft data-protection protocol, once ratified, could harmonize requirements, opening the door for governance platforms spanning multiple jurisdictions. Vendors able to certify compliance across divergent regimes stand to gain first-mover advantage.
Competitive Landscape
The market remains moderately fragmented. Global powerhouses such as Palo Alto Networks, Fortinet, and Cisco clinch bank and telecom deals by virtue of broad product suites and deep research budgets. Regional integrators like Dimension Data and BCX differentiate through local relationships, public-sector credentials, and the capacity to bolt professional and managed services onto multi-vendor stacks. Their proximity enables faster onsite support and cultural alignment, advantages especially valued by government departments.
Niche firms led by SensePost specialize in offensive security, providing red-teaming and vulnerability research that satisfy stringent audit requirements for financial institutions. Telecom operators, including Vodacom Business Security and MTN Business Security, cross-sell connectivity with managed firewalls and SD-WAN to create single-invoice convenience. Start-ups focusing on security automation for resource-limited teams are surfacing, yet venture-funding hurdles hamper scale-up. Artificial intelligence and machine-learning capabilities that cut false positives and shrink mean-time-to-detect are emerging battlefields; vendors that can prove operational savings are winning pilots.
ISO 27001 and SOC 2 Type II certifications have become entry tickets for managed service providers, as enterprises demand independent assurance before outsourcing critical monitoring. Price competition is intense for basic services, but vendors commanding specialized expertise such as industrial-control-system security or healthcare compliance achieve premium margins. Overall, buyer preference is tilting toward platform consolidation, so suppliers offering unified consoles for identity, endpoint, network, and cloud security are steadily eroding share from point-product incumbents.
South Africa Cybersecurity Industry Leaders
Check Point Software Technologies Ltd
Kaspersky Labs
Cisco Systems, Inc
Palo Alto Networks Inc.
CyberArk Software Ltd.
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- February 2026: Dimension Data, operating as NTT Ltd., invested ZAR 450 million (USD 24.8 million) to open a security operations center in Cape Town, expanding managed detection and response capacity.
- January 2026: Fortinet partnered with Vodacom Business to bundle FortiGate firewalls with fiber and 5G connectivity, delivering secure SD-WAN to mid-sized enterprises.
- December 2025: Microsoft injected ZAR 5.4 billion (USD 297 million) to enlarge Azure zones in Johannesburg and Cape Town, adding Sentinel and Defender for Cloud capabilities.
- November 2025: BCX Cybersecurity rolled out a managed extended detection and response subscription for SMEs starting at ZAR 15,000 (USD 825) per month.
South Africa Cybersecurity Market Report Scope
Cyber security utilizes technology, controls, and processes to protect systems, networks, programs, devices, and data against cyberattacks. Its purpose is to minimize the risk of cyber-attacks and to guard against unauthorized networks, systems, and technologies. Cybersecurity safeguards internet-connected systems from cyber threats such as hardware, software, and data. Individuals and corporations also use the technique to stop illegal access to data centers and other digital systems.
The South Africa Cybersecurity Market Report is Segmented by Offering (Solutions, and Services), Deployment Mode (On-Premise, and Cloud), End-use Industry (IT and Telecom, BFSI, Healthcare, Industrial Manufacturing, Retail and E-commerce, Energy and Utilities, Aerospace Military and Defense, and Other End-use Industries), End-User Enterprise Size (Large Enterprises, and Small and Medium Enterprises). The Market Forecasts are Provided in Terms of Value (USD).
| Solutions | Application Security |
| Cloud Security | |
| Data Security | |
| Identity and Access Management | |
| Infrastructure Protection | |
| Integrated Risk Management | |
| Network Security | |
| Endpoint Security | |
| Services | Professional Services |
| Managed Services |
| On-Premise |
| Cloud |
| IT and Telecom |
| BFSI |
| Healthcare |
| Industrial Manufacturing |
| Retail and E-commerce |
| Energy and Utilities |
| Aerospace, Military and Defense |
| Other End-use Industries |
| Large Enterprises |
| Small and Medium Enterprises (SMEs) |
| By Offering | Solutions | Application Security |
| Cloud Security | ||
| Data Security | ||
| Identity and Access Management | ||
| Infrastructure Protection | ||
| Integrated Risk Management | ||
| Network Security | ||
| Endpoint Security | ||
| Services | Professional Services | |
| Managed Services | ||
| By Deployment Mode | On-Premise | |
| Cloud | ||
| By End-use Industry | IT and Telecom | |
| BFSI | ||
| Healthcare | ||
| Industrial Manufacturing | ||
| Retail and E-commerce | ||
| Energy and Utilities | ||
| Aerospace, Military and Defense | ||
| Other End-use Industries | ||
| By End-User Enterprise Size | Large Enterprises | |
| Small and Medium Enterprises (SMEs) | ||


Key Questions Answered in the Report
What is the current value of the South Africa cybersecurity market?
It was USD 0.29 billion in 2025 and is projected to reach USD 0.59 billion by 2031.
How fast is spending on cloud-based security growing?
Cloud-delivered solutions are forecast to expand at a 13.64% CAGR between 2026 and 2031.
Which sector is expected to outpace others in new security investment?
Healthcare spending is set to grow the fastest, rising at a 14.11% CAGR on the back of electronic health record adoption.
Why are managed services becoming so popular among South African firms?
A national shortage of 30,000 cyber professionals and double-digit wage inflation push organizations toward outsourced detection, response, and compliance support.
How are regulators influencing security budgets?
Directive 8/2024 obliges banks to report incidents within 24 hours, while POPIA fines encourage encryption and data-loss-prevention rollouts, making cybersecurity a compulsory investment.
Page last updated on: