Cybersecurity Software Market Size and Share
Cybersecurity Software Market Analysis by ���ϲ�����
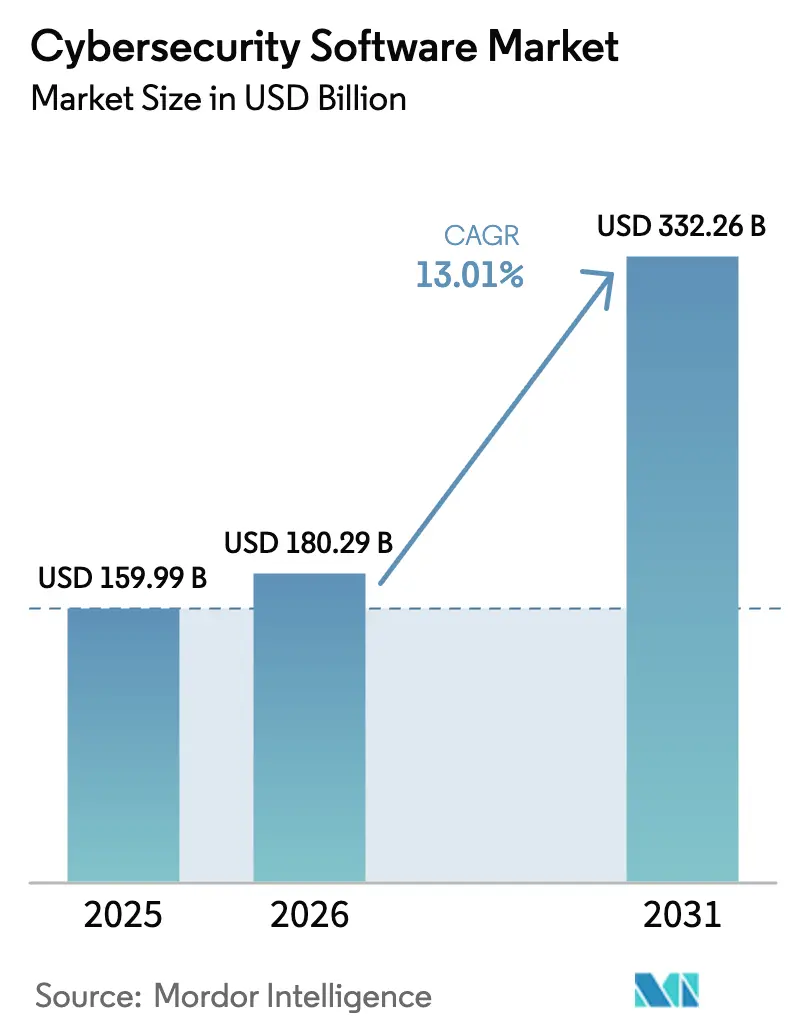
The cybersecurity software market size was valued at USD 159.99 billion in 2025 and is estimated to grow from USD 180.29 billion in 2026 to reach USD 332.26 billion by 2031, at a CAGR of 13.01% during the forecast period (2026-2031). Board-room perceptions have shifted, as executives now weigh cyber resilience alongside liquidity and solvency, directly linking security posture to enterprise value. Vendor roadmaps are increasingly shaped by global rule-making that tightens breach-disclosure windows, by the rapid spread of artificial intelligence in both attack and defense, and by the convergence of information-technology and operational-technology networks that extends the attack surface into factories and utility grids. Cloud-first strategies are forcing security to travel with workloads, creating sustained demand for cloud-native controls that inspect traffic, govern identities, and remediate misconfigurations in real time. Heightened cyber-insurance deductibles, paired with exclusion clauses that deny claims when basic controls are absent, have prompted even small firms to adopt managed detection and response, driving fresh growth across the cybersecurity software market.
Key Report Takeaways
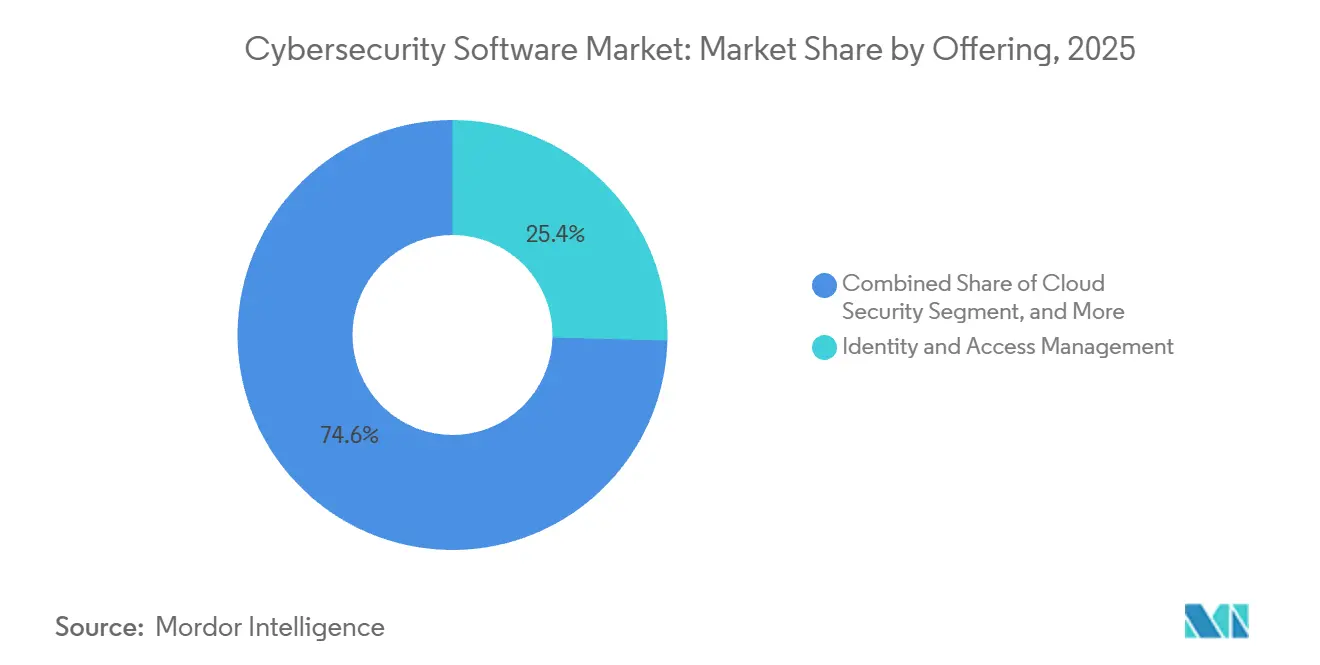
- By offering, identity and access management led with 25.41% share in 2025, while cloud security is advancing at a 14.43% CAGR through 2031.
- By deployment mode, the cloud-based segment captured 66.88% of the cybersecurity software market share in 2025 and is projected to expand at a 14.73% CAGR through 2031.
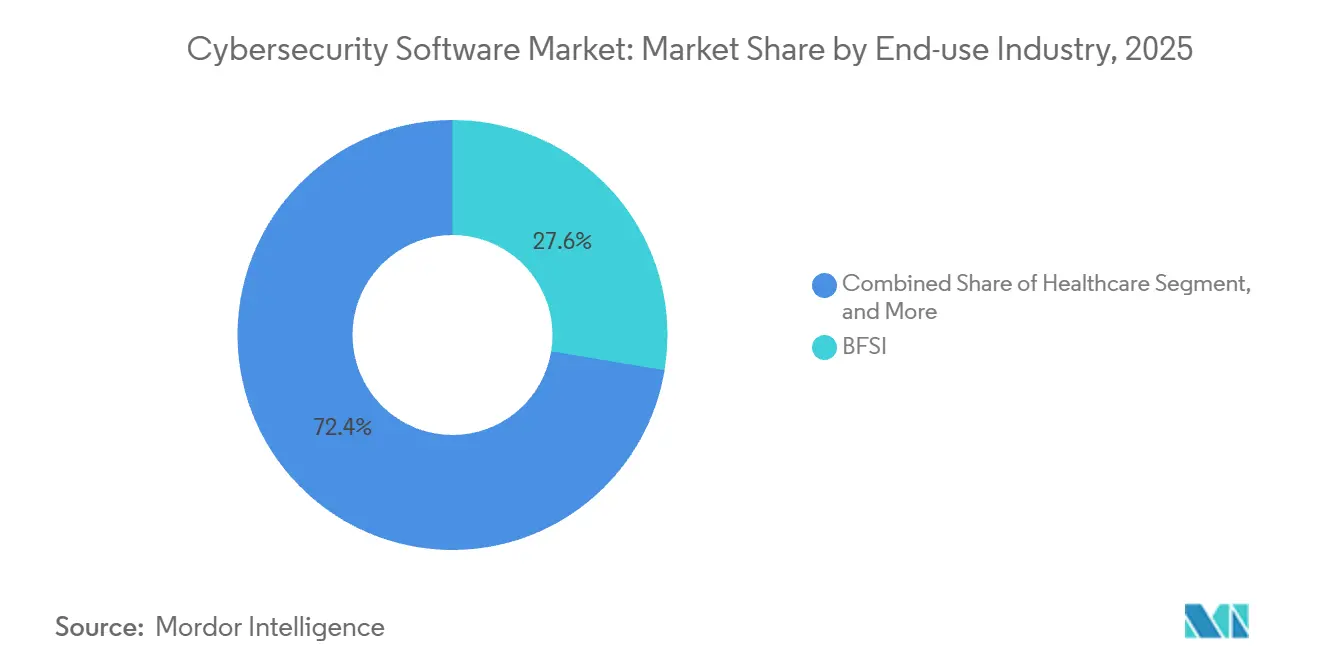
- By end-use industry, banking, financial services, and insurance accounted for 27.62% of the cybersecurity software market size in 2025, whereas healthcare registered the fastest growth at a 14.97% CAGR to 2031.
- By enterprise size, large enterprises dominated with a 63.17% share in 2025, yet the small and medium enterprises segment is forecast to rise at a 14.25% CAGR through 2031.
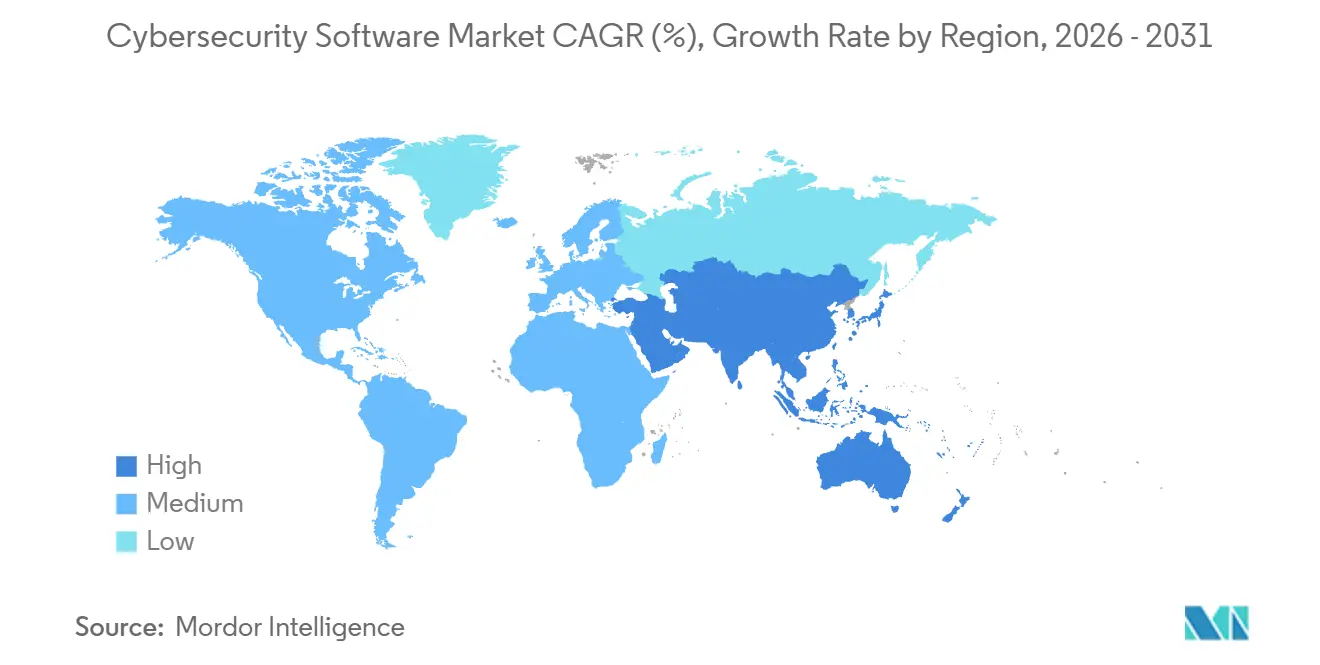
- By geography, North America retained a 38.65% share in 2025, and Asia-Pacific is projected to expand at a 15.01% CAGR during 2026-2031.
Note: Market size and forecast figures in this report are generated using ���ϲ�����’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
Global Cybersecurity Software Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Cloud-first Adoption and Zero-trust Mandates | +2.3% | Global, led by North America and Europe | Medium term (2-4 years) |
| Surge in AI-driven, Multi-vector Cyber-attacks | +2.1% | Global, concentrated in BFSI and Healthcare | Short term (≤ 2 years) |
| Escalating Regulatory Penalties for Cyber Incident Disclosure | +1.8% | North America and Europe, spill-over to Asia-Pacific | Short term (≤ 2 years) |
| OT and IT Convergence in Critical Infrastructure | +1.5% | Global, priority in Energy, Utilities, Manufacturing | Medium term (2-4 years) |
| Shift to API-centric Architectures Creating New Attack Surface | +1.2% | Global, led by IT and Telecom, Retail and E-commerce | Medium term (2-4 years) |
| Rising Cyber-insurance Premiums Drive Proactive Security | +0.9% | North America and Europe, emerging Asia-Pacific | Long term (≥ 4 years) |
| Source: ���ϲ����� | |||
Cloud-first Adoption and Zero-trust Mandates
Federal and corporate mandates are pushing organizations to replace perimeter-centric defenses with continuous verification that inspects every transaction regardless of location.[1]National Institute of Standards and Technology, “Special Publication 1800-35: Implementing a Zero Trust Architecture,” nist.gov Executive Order 14144 obliges U.S. civilian agencies to implement identity governance, micro-segmentation, and phishing-resistant authentication by fiscal 2027, setting a procurement baseline that resonates in the private sector. Cloud migration amplifies the urgency because workloads, data, and users disperse across multiple service providers, making software-defined perimeters, cloud security posture management, and workload protection essential. The Office of Management and Budget’s zero-trust maturity model requires continuous diagnostics that feed into security information and event management, accelerating demand for endpoint detection integrations. Vendors capable of orchestrating least-privilege access across hybrid infrastructure have gained momentum, thereby expanding the cybersecurity software market.
Surge in AI-driven, Multi-vector Cyber-attacks
Threat actors are weaponizing generative AI to automate reconnaissance, craft adaptive phishing, and launch polymorphic malware that evades static signatures. IBM X-Force recorded a 42% jump in attacks that blend ransomware, data exfiltration, and distributed denial-of-service tactics, forcing defenders to correlate signals across vectors.[2]IBM Security, “X-Force Threat Intelligence Index 2026,” ibm.com Deepfake-enabled executive impersonation caused losses exceeding USD 1 billion in 2025, according to the FBI Internet Crime Complaint Center, elevating board concern over social-engineering resiliency. Security teams are embedding machine-learning analytics within security operations centers to triage alerts and surface anomalous behaviors indicative of privilege escalation. Regulatory bodies, such as the National Security Agency, explicitly recommend AI-driven user and entity behavior analytics, signaling that baseline compliance now includes machine learning.
Escalating Regulatory Penalties for Cyber Incident Disclosure
The U.S. Securities and Exchange Commission requires public companies to disclose material cyber incidents within four business days, shrinking the interval between detection and stakeholder notification.[3]U.S. Securities and Exchange Commission, “SEC Charges Four Companies with Misleading Cyber Disclosures,” sec.gov Multi-million-dollar penalties levied in 2024 and 2025 against firms that mis-stated breach impacts demonstrate that enforcement has teeth. Additional amendments to Regulation S-P oblige financial institutions to encrypt customer data and notify clients within 30 days of unauthorized access, propelling demand for governance, risk, and compliance platforms that embed audit trails. Boards consequently seek automated incident-response and forensic readiness tools to meet stringent timelines, reinforcing growth in the cybersecurity software market.
OT and IT Convergence in Critical Infrastructure
Industrial firms are integrating operational technology networks with enterprise IT systems for predictive maintenance and analytics, but this convergence exposes controllers, sensors, and safety systems to mainstream cyber threats. January 2026 guidance mandates segmentation and continuous monitoring across industrial control networks, while Microsoft found a 60% rise in attacks aimed at programmable logic controllers. Sector standards such as ISA/IEC 62443 have become procurement prerequisites, driving asset inventory, vulnerability management, and protocol-aware detection spending. Energy, utilities, and manufacturing organizations now steer vendor selection toward platforms that ingest Modbus, DNP3, and proprietary telemetry, broadening addressable revenue for the cybersecurity software market.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Persistent Talent Deficit and Wage Inflation | -1.4% | Global, acute in North America and Europe | Long term (≥ 4 years) |
| Tool Sprawl Causing ROI Fatigue in C-suites | -1.1% | Global, concentrated in Large Enterprises | Medium term (2-4 years) |
| Legacy Technical Debt in Public Sector and SMBs | -0.8% | Global, pronounced in Public Sector and SMBs | Long term (≥ 4 years) |
| Sovereign-cloud and Data-residency Conflicts | -0.6% | Asia-Pacific, Middle East, select European jurisdictions | Medium term (2-4 years) |
| Source: ���ϲ����� | |||
Persistent Talent Deficit and Wage Inflation
The global shortfall of four million skilled professionals strains implementation timelines, as cloud security architects, threat hunters, and SOC managers command double-digit annual wage growth. National training frameworks add new competencies faster than universities can update curricula, leaving enterprises dependent on managed security services or automation to plug gaps. While automation lowers alert volume, onboarding and tuning advanced platforms still require expert oversight, prolonging return-on-investment cycles and tempering overall expansion of the cybersecurity software market.
Tool Sprawl Causing ROI Fatigue in C-suites
Large enterprises operate as many as 60 discrete security tools, which inflates licensing costs and consumes analyst bandwidth in alert correlation. Executives increasingly demand proof that each incremental product measurably reduces residual risk before allocating new budget, slowing purchase decisions. Vendors are answering with consolidated extended detection and response suites, yet migration entails retraining staff and rewriting playbooks, introducing temporary coverage gaps that some risk-averse firms postpone. This friction weighs on the growth trajectory of the cybersecurity software market, even as consolidation promises eventual efficiency gains.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Segment Analysis
By Offering: Identity Governance Anchors Zero-trust Transition
Identity and Access Management accounted for 25.41% of the share in 2025, underscoring its primacy in zero-trust blueprints that require continuous authentication for every session. This slice of the cybersecurity software market size confirms that credential and device trust signals sit at the policy core of modern architectures. Adoption of hardware tokens and biometric passkeys accelerated after the National Institute of Standards and Technology guidelines deprecated the use of SMS one-time passwords, while privileged access vaulting expanded into DevOps pipelines to protect secrets during software builds. Cloud Security, growing at a 14.43% CAGR through 2031, benefits from multi-cloud deployments that demand posture management, workload protection, and API inventory scanning, thereby diversifying revenue beyond traditional gateways.
Application Security is advancing as development teams embed static, dynamic, and software composition analysis in continuous integration pipelines, integrating findings into agile backlogs for faster remediation. Network Security products are morphing into secure access service edge frameworks that converge connectivity and protection within cloud points of presence, a model that supports roaming employees without backhauls. Endpoint Security vendors integrate telemetry with network and identity signals to deliver extended detection on a single console, reducing analyst swivel-chair time. Data Security and Integrated Risk Management suites round out portfolios by encrypting sensitive fields, tokenizing regulated attributes, and surfacing executive dashboards that quantify risk in monetary terms all catalysts for the broader cybersecurity software market.

By Deployment Mode: Cloud Platforms Dominate Elastic Workloads
Cloud deployments commanded 66.88% share in 2025 and will expand at a 14.73% CAGR through 2031 as elastic infrastructure becomes default. Remote work rendered location-based controls obsolete, steering organizations toward cloud-native secure web gateways, cloud access security brokers, and zero-trust network access services that enforce uniform policy anywhere. Vendors leverage aggregated telemetry to train machine-learning engines, updating customer defenses without hardware swaps, a capability on-premise appliances cannot match. The cybersecurity software market share gap between cloud and on-premise implementations is therefore set to widen during the forecast window.
On-premise stacks persist where data residency, air-gapped mandates, or legacy assets dictate full custodianship. Defense contractors, critical infrastructure operators, and public agencies with classified workloads maintain private clouds or containerized instances inside controlled environments. Hardware refresh cycles and specialized skill requirements inflate on-premise total cost of ownership, yet certain workloads, such as industrial control system monitoring or high-frequency trading, still demand latency guarantees unobtainable over commodity internet circuits. Hybrid approaches that keep crown-jewel data in customer-owned data centers while shifting analytics to SaaS offer a transitional path, sustaining a diversified deployment mix within the cybersecurity software market.
By End-use Industry: Healthcare Ransomware Accelerates Spending
Banking, Financial Services, and Insurance led with 27.62% of share in 2025, a dominance rooted in high-value data and stringent regulation. Post-breach fines under the Digital Operational Resilience Act and other regimes catalyze investment in governance, risk, and compliance modules alongside detection controls. Healthcare, forecast to advance at a 14.97% CAGR, faces escalating ransomware attacks that interrupt care delivery and jeopardize patient safety, forcing hospitals to implement network segmentation, offline backups, and vulnerability management tuned to medical devices. These dynamics enlarge the patient safety remit of cybersecurity, deepening the addressable cybersecurity software market.
IT and Telecom firms guard latency-sensitive networks against distributed denial-of-service floods, while Retail and E-commerce deploy fraud detection and encryption to satisfy PCI DSS 4.0. Industrial Manufacturing and Energy players harden programmable logic controllers after high-profile shutdowns demonstrated that cyber-physical attacks carry direct revenue and safety impacts. Aerospace, Military, and Defense contractors align investments with Cybersecurity Maturity Model Certification levels, which now influence procurement eligibility, cementing cyber readiness as table stakes for federal contracts.

By End-User Enterprise Size: SMEs Adopt Managed Services
Large Enterprises absorbed 63.17% of share in 2025, leveraging purchasing power to negotiate enterprise agreements that bundle multiple product families. Those conglomerates demand granular policy engines that integrate with asset inventories and workflow orchestration, compelling vendors to expose open APIs and custom reporting features. Small and Medium Enterprises, growing at a 14.25% CAGR, rely on managed security service providers for 24/7 monitoring and incident response, circumventing the talent drought. Insurers refuse or surcharge policies lacking multi-factor authentication and endpoint detection, effectively mandating a minimum security baseline that drives fresh adoption across the cybersecurity software market.
Cloud SaaS subscription tiers lower entry barriers, letting SMEs buy enterprise-grade controls without capex. Yet SMEs struggle with policy fine-tuning and response playbooks, inviting simplified, wizard-driven interfaces that hide complexity. Vendors targeting this cohort emphasize rapid deployment, automated configuration, and pay-as-you-use billing, whereas enterprise-class offerings prioritize extensibility and custom integrations, preserving a bifurcated product landscape under the single umbrella of the cybersecurity software industry.
Geography Analysis
North America retained 38.65% of the cybersecurity software market in 2025, underpinned by Executive Order 14144 that mandates zero-trust architectures across federal agencies and by SEC rules that compress incident-reporting windows. Financial services, healthcare, and cloud-native technology firms in the United States grapple with an outsized share of ransomware and intellectual-property theft, sustaining demand for extended detection, identity governance, and risk quantification platforms. Canada’s updated privacy statute, with compulsory breach notification, drives data loss prevention uptake, while Mexico’s expanding automotive and electronics corridors invest in operational-technology security to safeguard just-in-time production lines.
Asia-Pacific is projected to grow at a 15.01% CAGR through 2031, benefiting the cybersecurity software market as national regulations multiply. China enforces data localization and critical-infrastructure assessments, prompting investments in sovereign clouds and on-premise encryption. India’s six-hour breach-reporting rule accelerates adoption of security information and event management platforms and cloud workload protection across domestic and multinational enterprises. Japan’s strategy prioritizes supply-chain assurance, channeling funding toward vulnerability management, while ASEAN coordination frameworks stimulate cross-border threat-intelligence sharing that requires interoperable APIs.
Europe’s cybersecurity software market expands on the back of the Network and Information Security Directive 2 and the Digital Operational Resilience Act, both of which impose rigorous controls on operators of essential services and financial entities. Record GDPR penalties exceeding EUR 2 billion (USD 2.26 billion) in 2024-2025 incentivize encryption, tokenization, and third-party risk assessment. The United Kingdom’s cloud-security principles guide procurement toward zero-trust and continuous monitoring. South America adopts privacy statutes that spur consent management platforms, while Middle Eastern nations back sovereign cloud data centers and workforce skilling initiatives. Africa contributes emergent growth through mobile banking security in Nigeria, Egypt, and South Africa.
Competitive Landscape
Competition centers on platform consolidation as chief information security officers strive to trim redundant tools and unify telemetry. Transactional highlights include Palo Alto Networks’ purchase of IBM’s QRadar SaaS assets, Microsoft’s bundling of endpoint, identity, and cloud defenses into Defender, and Cisco’s addition of secure access service edge to existing network franchises, indicating that big-cap vendors aim to secure a larger slice of the cybersecurity software market. Customers value single-console visibility because it trims alert fatigue and administrative overhead, yet best-of-breed niches endure where specialized functionality outpaces platform roadmaps, such as operational-technology anomaly detection or quantum-safe cryptography.
Artificial intelligence differentiates winners; CrowdStrike mines two trillion weekly events to train behavior models that halt lateral movement, while SentinelOne’s autonomous rollback neutralizes ransomware without manual intervention. Forward-looking roadmaps address security for AI model pipelines, decentralized finance ledgers, and quantum-era key exchange. International standard-setting, including ISO’s AI-security guidelines and NIST’s post-quantum cryptography project, foreshadows new compliance mandates that will open adjacent revenue pools.
Mid-tier vendors accelerate go-to-market through managed security services, partnering with telecommunications carriers and global system integrators to access small and mid-market customers that lack internal staff. Talent scarcity raises operating expense, so vendors invest in regional security operations centers that deliver 24/7, follow-the-sun coverage, as evidenced by Fortinet’s Singapore and Poland expansions. Sovereign-cloud restrictions create fragmentation, compelling providers to deploy regional data-plane instances, yet offer differentiation for firms able to certify local compliance. Overall, the cybersecurity software market remains moderately concentrated, with the top ten companies holding roughly one-half of global revenue, leaving space for innovators that specialize in emerging threat vectors.
Cybersecurity Software Industry Leaders
IBM Corporation
Microsoft Corporation
Cisco Systems Inc.
Check Point Software Technologies Ltd.
Broadcom Inc. (Symantec Enterprise Division)
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- February 2026: Microsoft announced the general availability of Microsoft Security Copilot, an AI assistant that automates threat investigation and remediation by correlating telemetry across endpoints, identities, and clouds.
- January 2026: Palo Alto Networks completed the USD 500 million acquisition of IBM’s QRadar SaaS business, rolling SIEM capabilities into the Cortex XSIAM platform for unified extended detection.
- December 2025: CrowdStrike launched Falcon Cloud Security, integrating posture management, workload protection, and container security to streamline multi-cloud defense.
- November 2025: Fortinet committed USD 300 million to expand security operations centers in Singapore and Poland, adding 24/7 monitoring services aimed at talent-constrained customers.
Global Cybersecurity Software Market Report Scope
The cybersecurity software market is defined based on the revenues generated from the software used in various end-user industries across the globe. The analysis is based on the market insights captured through secondary research and the primaries. The market also covers the major factors impacting its growth in terms of drivers and restraints. The study tracks the key market parameters, underlying growth influencers, and major vendors operating in the industry, which support the market estimations and growth rates over the forecast period.
The Cybersecurity Software Market Report is Segmented by Offering (Application Security, Cloud Security, Data Security, Identity and Access Management, Infrastructure Protection, Integrated Risk Management, Network Security, and Endpoint Security), Deployment Mode (On-Premise, and Cloud), End-use Industry (IT and Telecom, BFSI, Healthcare, Industrial Manufacturing, Retail and E-commerce, Energy and Utilities, Aerospace, Military and Defense, and Other End-use Industries), End-User Enterprise Size (Large Enterprises, and Small and Medium Enterprises), and Geography (North America, South America, Europe, Asia-Pacific, and Middle East and Africa). The Market Forecasts are Provided in Terms of Value (USD).
| Application Security |
| Cloud Security |
| Data Security |
| Identity and Access Management |
| Infrastructure Protection |
| Integrated Risk Management |
| Network Security |
| Endpoint Security |
| On-Premise |
| Cloud |
| IT and Telecom |
| BFSI |
| Healthcare |
| Industrial Manufacturing |
| Retail and E-commerce |
| Energy and Utilities |
| Aerospace, Military and Defense |
| Other End-use Industries |
| Large Enterprises |
| Small and Medium Enterprises (SMEs) |
| North America | United States | |
| Canada | ||
| Mexico | ||
| South America | Brazil | |
| Argentina | ||
| Rest of South America | ||
| Europe | Germany | |
| United Kingdom | ||
| France | ||
| Italy | ||
| Spain | ||
| Rest of Europe | ||
| Asia-Pacific | China | |
| Japan | ||
| India | ||
| South Korea | ||
| Australia | ||
| Southeast Asia | ||
| Rest of Asia-Pacific | ||
| Middle East and Africa | Middle East | Saudi Arabia |
| United Arab Emirates | ||
| Turkey | ||
| Rest of Middle East | ||
| Africa | South Africa | |
| Nigeria | ||
| Egypt | ||
| Rest of Africa | ||
| By Offering | Application Security | ||
| Cloud Security | |||
| Data Security | |||
| Identity and Access Management | |||
| Infrastructure Protection | |||
| Integrated Risk Management | |||
| Network Security | |||
| Endpoint Security | |||
| By Deployment Mode | On-Premise | ||
| Cloud | |||
| By End-use Industry | IT and Telecom | ||
| BFSI | |||
| Healthcare | |||
| Industrial Manufacturing | |||
| Retail and E-commerce | |||
| Energy and Utilities | |||
| Aerospace, Military and Defense | |||
| Other End-use Industries | |||
| By End-User Enterprise Size | Large Enterprises | ||
| Small and Medium Enterprises (SMEs) | |||
| By Geography | North America | United States | |
| Canada | |||
| Mexico | |||
| South America | Brazil | ||
| Argentina | |||
| Rest of South America | |||
| Europe | Germany | ||
| United Kingdom | |||
| France | |||
| Italy | |||
| Spain | |||
| Rest of Europe | |||
| Asia-Pacific | China | ||
| Japan | |||
| India | |||
| South Korea | |||
| Australia | |||
| Southeast Asia | |||
| Rest of Asia-Pacific | |||
| Middle East and Africa | Middle East | Saudi Arabia | |
| United Arab Emirates | |||
| Turkey | |||
| Rest of Middle East | |||
| Africa | South Africa | ||
| Nigeria | |||
| Egypt | |||
| Rest of Africa | |||


Key Questions Answered in the Report
How large will spending on cybersecurity software be by 2031?
It is forecast to reach USD 332.26 billion in 2031, rising at a 13.01% CAGR from 2026 through 2031.
Which solution category currently leads organizational budgets?
Identity and Access Management commands the largest share at 25.41% of share in 2025 because it forms the control plane of zero-trust architectures.
Why is cloud deployment growing faster than on-premise alternatives?
Cloud-based delivery offers elastic scaling, global reach, and frictionless updates, helping it secure 66.88% share in 2025 and expand at a 14.73% CAGR to 2031.
What sector is expected to grow the fastest between 2026 and 2031?
Healthcare shows the highest projected CAGR at 14.97%, driven by ransomware attacks that threaten patient safety and continuity of care.
How are new regulations influencing vendor selection?
Rules such as SEC four-day incident disclosure and the Digital Operational Resilience Act require automated reporting, encryption, and continuous monitoring, making integrated platforms more attractive to compliance teams.
Page last updated on: